QV version 20240423 pre-alpha released
Please read the 20240419 announcement:
https://bkhome.org/news/202404/qv-version-20240419-pre-alpha-released.html
Since then, there have been bug fixes, see the forum:
https://forum.puppylinux.com/viewtopic.php?t=11292
Also enhancements, see:
https://bkhome.org/news/202404/shell-wrapper-for-sudo.html
https://bkhome.org/news/202404/qv-snapshot-information-on-desktop.html
Bluetooth and samba fixed, among other fixes.
Still no update mechanism. Hope to do that for the next release.
Thereafter, no more need to download the huge .img file, just
install a small update PET.
Tags: quirky
Shell wrapper for sudo
I posted about sudo here:
https://forum.puppylinux.com/viewtopic.php?p=117577#p117577
Which has brought this issue back to my attention. I really don't know why sudo was working and then it wasn't.
Anyway, I developed a simple alternative, named 'sudo-sh', see these blog posts mid-2023:
https://bkhome.org/news/202306/goodbye-sudo-package.html
https://bkhome.org/news/202306/light-weight-replacement-for-sudo.html
But what about an app that calls the sudo executable? EasyOS doesn't have sudo, QV does but it doesn't work.
To fix this, I created a shell script named 'sudo'. I don't know if an app will refuse to run it, if it sees it isn't a binary executable, or doesn't have suid bit set. Also, it ignores all commandline options. Anyway, here it is, /usr/bin/sudo:
#!/bin/ash
C=''
while [ -n "$1" ];do
case "$1" in
-*)
case "$1" in
-g|-p|-U|-u|-C|-r|-t)
shift
;;
esac
;;
*)
C="$@"
;;
esac
shift
done
if [ -n "$C" ];then
exec sudo-sh ${PPID} ${C}
fi
This will only work in EasyOS and QV, that have sudo-sh. A simple test:
# su spot
# sudo urxvt
...a window pops up asking for the root password, then the urxvt terminal runs.
That sudo script is very simple, could be written in C.
Tags: quirky
QV snapshot information on desktop
Users of QV are likely to make heavy use of the btrfs snapshot feature. I have posted about QV's support for snapshots, see here:
https://bkhome.org/news/202404/qv-snapshot-deletion.html
What seems to be needed is "at a glance" information about what snapshot is currently running. I have implemented that information, written to the wallpaper, in format snapshot-number: creation-date: description.
At the first bootup, I have set the decription as "Original Snapshot", though it is not a snapshot as such, but the originator of snapshots. This description will also be translated if the user selects a non-English language.
Here is what it looks like, along the top of the desktop:

Here is the github commit:
https://github.com/bkauler/woof-quantum-vis/commit/f13a1f913fbd1409b34e03def05d33c8bfc50bc1
...using GraphicsMagick to write the text on the
image.
Tags: quirky
QV version 20240419 pre-alpha released
QV is a new very experimental Linux distribution, under development and still evolving. To read about what has happened so far, follow the blog posts with the "quirky" tag:
https://bkhome.org/news/tag_quirky.html
In a nutshell, QV has many features of EasyOS, except does not have a layered filesystem, nor SFS files. It is a "frugal full" installation, built from Void Linux packages using the XBPS package manager. It also has some EasyOS Kirkstone .tar.xz and PET packages. Another very significant feature is that QV is installed in a btrfs filesystem, with support for compression and snapshots.
I have been playing with a logo; this is the latest:

The letters "QV" may mean "Quirky Void", as this is a very quirky distribution compared with Void Linux. Or, it may mean "Quantum Vis", which is Latin for "has everything that you need".
Download from here:
https://distro.ibiblio.org/easyos/amd64/releases/void/
You can write the drive-image file to a USB Flash drive and boot that. Or, it can be installed directly to an internal HDD or SSD; with some caveats. See forum post for details:
https://forum.puppylinux.com/viewtopic.php?t=11292
If you look at the 'qv-installer' script, also at 'limine.cfg' in the drive-image file, you will see that "BOOT_UUID" and "BOOT_DIR" kernel parameters are now required, as well as WKG_UUID and WKG_DIR. The reason for this is that 'vmlinuz' and 'initrd' may be in a different partition than the working-partition, and an "update" operation will need to know where they are.
As there are no longer SFS files, the "devx" is now a PET package. It can be installed via PKGget, or downloaded directly from here:
https://distro.ibiblio.org/easyos/amd64/packages/pet/pet_packages-void/
In the latter case, right-click on it and choose "petget" from
the menu.
'devx-240419.pet' is a "meta package". What that means is that it doesn't contain any packages, just a 'pinstall.sh' script that will install everything required to setup a development environment. I suggest, take a snapshot first, before installing it, with an appropriate name, like "devx development evironment". Then, before doing any actual compiling, take a snapshot of the snapshot, to retain a pristine devx environment.
I'm not sure, but I think best to run "xbps-install -S" first, before installing the devx PET, to sync with the remote repositories.
XBPS will download 624 packages, a total of 592MB, so be prepared for it to take awhile.
After install has finished, delete /etc/profile.d/gawk.csh and /etc/profile.d/gawk.sh -- these are broken.
If you want to install with "new2dir make install", the 'installwatch' package is required. Download it from here:
...download, right-click and choose "petget" to install it.
You will notice that there is no longer an "update" icon on the desktop. This is because updating will mostly be done via XBPS. It is intended that there will also be a kernel PET and an update PET that will have fixes.
This update strategy has yet to be implemented. It will mean that you only have to download the big .img file once, and there-after rely on XBPS to update packages, and kernel and patch PETs.
Feedback welcome at the forum.
EDIT 2024-04-23
Superceded by version 240423, see announcement:
https://bkhome.org/news/202404/qv-version-20240423-pre-alpha-released.html
Tags: quirky
More /etc/init.d replacements for runit
QV, like EasyOS, and before that Quirky and the various pups that I maintained, uses the simple busybox init, with start/stop scripts in /etc/init.d. Except, for QV and EasyOS, there is service management with enhanced pup_event.
Void Linux uses runit to manage services. QV is capable of launching the runit daemon and using runit; however, I would prefer to stay with /etc/init.d, as it is very simple and works flawlwessly. Besides, it is what I know.
woofQV, the QV builder, has a 'packages-templates' directory that can modify any package installation. I have anticipated future packages that a user might want to install, and added /etc/init.d scripts where needed to replace runit.
Here is the commit:
https://github.com/bkauler/woof-quantum-vis/commit/507ebfad912b7a32f237ca147aa33d8228608744
Note, I got all of these from OpenEmbedded.
Tags: quirky
QV snapshot deletion
About two weeks ago, I posted about btrfs snapshot management in QV:
https://bkhome.org/news/202404/qv-snapshot-management.html
I have now added deletion of snapshots. There is a new item in the menu:
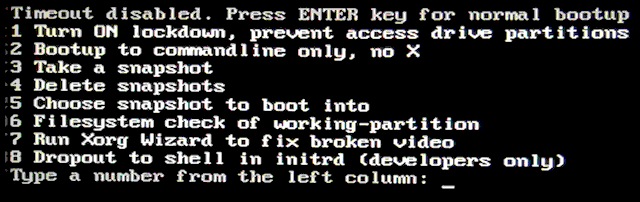
Choosing item-4:
...snapshot #1 is missing, because that s the current default that will be booted into. Whatever is the current default will be filtered-out.
From a bit of online reading, it seems that deleting snapshots can take awhile. For that reason, the children of each snapshot are listed. For example, snapshots 3 and 5 are snapshots of number 2. Number 4 is a snapshot of 3. My reasoning is that snapshots that have children, especially children-of-children, are likely to require a lot more processing to delete.
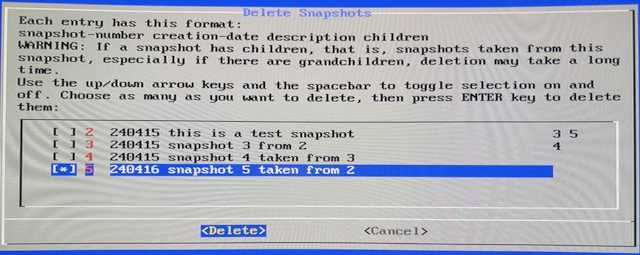
I have selected number 5, and the next window:
There wasn't much processing to delete it, took the blink of an eye, then this window:
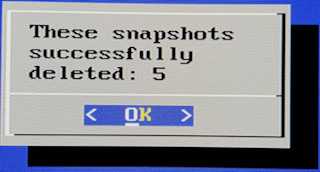
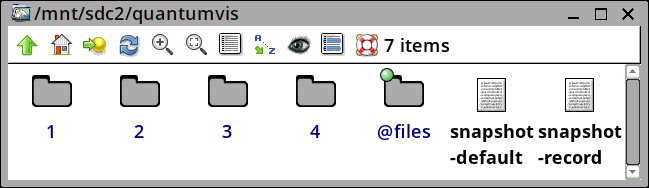
After bootup, it is seen that folder "5" is now gone:
Looking good!
Tags: quirky
QV version 240409 pre-alpha uploaded
Download from here:
https://distro.ibiblio.org/easyos/amd64/releases/void/
The md5sum is:
87a22559d5d7b414e810dbf2d7e36ae3
It is a bit bigger than the previous release, 1.3GB up from 1.1GB. The reason is have set zstd to compression level 3, whereas before it was 15. Want to see if it makes a noticeable difference in app startup time. ...for Firefox on my old Compaq Presario, not noticeably faster.
You will notice that the logo is just the letter "Q". That is just a whimsical thing I tried, wanted to see what it looks like in use ...no, doesn't really "work".
If you want to do a frugal install direct to internal drive, and not bootup QV first on a usb-stick, can do. There is a script, 'qv-installer', that should work on most Linux distros. You will also need the 'mount-img' script. I will post the latest of these two scripts to the forum, here:
https://forum.puppylinux.com/viewtopic.php?p=116553#p116553
Grab those two scripts, remove the false ".gz", set as executable, and put them in /usr/bin or anywhere in the $PATH.
You then need to download 'qv-240409-amd64.img' and open a terminal where-ever it is downloaded to, then run, as the root user:
# qv-installer qv-240409-amd64.img
The script will check that you have all the required utilities and packages installed. For example, 'btrfs-progs' package.
Have fun, feedback welcome at the forum.
Oh yeah, the "update" icon on the desktop. That doesn't work. I
have yet to figure out a strategy for updating.
Tags: quirky
New QV Installer
Easy install to an internal drive. Announced in forum post:
https://forum.puppylinux.com/viewtopic.php?p=116393#p116393
The script is part-manual, part-automatic. Not as sophisticated
as installers in the mainline distros.
Tags: quirky