FlatOrange desktop icon theme updated
The FlatOrange desktop icon theme is at /usr/local/lib/X11/themes/FlatOrange. It is builtin in woofQ2. It was created a very long time ago, in the very early Puppy Linux days, and was lacking some icons now required in EasyOS. Forum member retiredt00 has fixed that:
https://forum.puppylinux.com/viewtopic.php?p=169653#p169653
We do have a lot of old PET packages that are in the same boat, see "desk_icon_theme*" packages:
https://distro.ibiblio.org/easyos/noarch/packages/pet/pet_packages-noarch/
...look at the dates, see how old some of them
are.
Tags: easy
gtk2-ng introspection compile fix
Easy 7.3.9 has gtk-ng, compiled with "--introspection=no". This was raised as an issue:
https://git.devuan.org/Daemonratte/gtk2-ng/issues/21
Great, now fixed.
We have been discussing gtk2-ng in the forum:
https://forum.puppylinux.com/viewtopic.php?t=16898
Tags: easy
EasyOS Excalibur-series version 7.3.9 released
This is a release-candidate for 7.4, marking a fundamental commitment to a "legacy" architecture, embracing Xlibre and gtk2-ng. And, finally successful, supporting Sound Open Firmware (SOF), so audio will work on very modern computers.
Changes since 7.3.8:
- EasyOS built with gtk2-ng — June 08, 2026
- ROX-Filer video thumbnails — June 08, 2026
- Kernel 6.12.92 compiled with SOF enabled — June 07, 2026
- Alternative method to build EasyOS with Xlibre — June 05, 2026
- Xlibre video drivers compiled in EasyOS — June 05, 2026
- Xlibre input drivers compiled in EasyOS — June 05, 2026
- Xlibre server and drivers compiled in EasyOS — June 05, 2026
- Chromium 149.0.7827.53
Note, not built with excalibur-backports repository (as
is version 7.3.8).
ROX-Filer is one of our fantastic gtk2-based apps, and we have been on a roll enhancing it; the latest feature is video-thumbnails. We intend that a lot of other excellent but neglected gtk2-based apps will find their way into EasyOS.
Release notes, showing details of past releases:
https://distro.ibiblio.org/easyos/amd64/releases/excalibur/2026/7.3.9/release-notes.htm
Download the drive image file:
https://distro.ibiblio.org/easyos/amd64/releases/excalibur/2026/7.3.9/
If you are a newcomer to EasyOS, please read the version 7.3 announcement, as it has more getting-started information:
- EasyOS Excalibur-series version 7.3 released — April 26, 2026
Also, an overview of how and why EasyOS is unique:
https://easyos.org/about/how-and-why-easyos-is-different.html
The change to an SOF-enabled kernel brings with it some trepidation, given past troubles. Let me know if you experience any audio issues, like no sound or some input or output channels being wrong.
Hopefully, we will just fix and tweak a few things, then with great fanfare release version 7.4!
Feedback welcome at the forum:
https://forum.puppylinux.com/viewtopic.php?p=171787#p171787
Have fun!
Tags: easy
EasyOS built with gtk2-ng
Posted a couple of days ago, the next release of EasyOS will be built with Xlibre, replacing Devuan's X11 packages. GTK version 2 has also been revived, the project is named "gtk2-ng", here:
https://git.devuan.org/Daemonratte/gtk2-ng
I have compiled it in woofQ2; however had to configure with "--enable-introspection=no". Raised an issue:
https://git.devuan.org/Daemonratte/gtk2-ng/issues/21
...undefined symbols, looks like a header file is missing somewhere.
Anyway, going ahead with putting this into the next release of
Easy, without the gobject introspection; currently no gtk2-based
apps need it, none being builtin to Easy anyway. There are some
python-based apps that need introspection, but they are using
gtk3.
Tags: easy
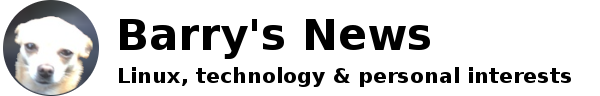
ROX-Filer video thumbnails
I recently received an email from Rick, reminding me that he would very much like if ROX supports video thumbnails. I vaguely recall, someone else on the forum also made this request. Personally, I had no interest, so let it slide, until now.
How to do it is described in the original ROX User Manual:
https://rox.sourceforge.net/Manual/Manual/Manual.html#id2504872
However, we found that it doesn't work. We have discussed the problem in the forum, and we found that the Jun7 fork of ROX does work, but the original source, the woof-CE source, and my own fork of ROX in woofQ2, do not. Forum member Burunduk found the reason, that the .png thumbnails need metadata:
https://forum.puppylinux.com/viewtopic.php?t=16991
Excellent, but I found that my fork used in EasyOS still doesn't work; which narrowed down to a particular source patch. Took out the patch, and now works. We will examine that patch sometime in the future. Anyway, now working in EasyOS:
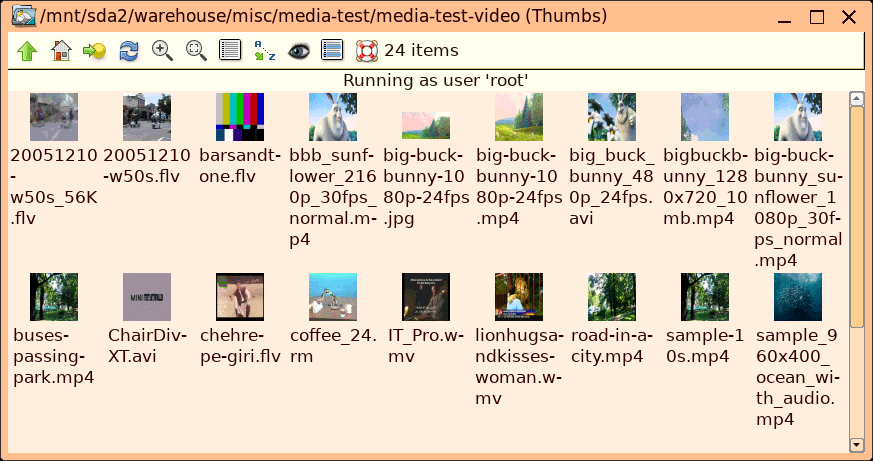
ROX looks for scripts in /etc/xdg/rox.sourceforge.net/MIME-thumb
to generate the thumbnails.
For example, script 'video_mp4':
#!/bin/sh
# $1-path to source, $2-path to output, $3-pixel size
exec ffmpegthumbnailer -i "${1}" -s ${3} -t 10 -q 8 -a -m -o ${2}
...ffmpegthumbnailer is a little binary executable, available via
PKGget. All of this will be in the next release of Easy.
This is a nice feature to have. We are on a roll recently,
improving ROX, so this is one more.
Tags: easy
Kernel 6.12.92 compiled with SOF enabled
Yes, having another go! Here is blog post about the previous attempt:
- SOF fail trying again — May 25, 2026
Forum member NNI has compiled the kernel and reports success:
https://forum.puppylinux.com/viewtopic.php?p=171595#p171595
I have used basically the same kernel config, except disabled some "Kernel hacking" debug features. I doubt that Sound Open Firmware would require them, and one of them, CONFIG_LOCKDEV, caused the Broadcom "wl" module compile to fail, with "GPL only symbol: lockdep_init_map_type"
Interesting, in a previous blog post I reported using a script
from the SOF project site, to determine what to enable in the
'.config' file, and it enabled lots of kernel debugging features.
Which I have now disabled. But, very odd, the script failed to
enable what NNI found to be essential for SOF to work;
CONFIG_SND_SOC_INTEL_SOUNDWIRE_LINK_BASELINE.
The '.config' file will be in woofQ2 when I next upload it, also
uploaded separately here,
with false ".gz" appended.
Tags: easy
Alternative method to build EasyOS with Xlibre
Continuing a series of blog posts how Xlibre was compiled in
EasyOS:
- Xlibre video drivers compiled in EasyOS — June 05, 2026
- Xlibre input drivers compiled in EasyOS — June 05, 2026
- Xlibre server and drivers compiled in EasyOS — June 05, 2026
An earlier post described how Xlibre was builtin to EasyOS 7.3.8:
- EasyOS built with Xlibre — June 02, 2026
...in a nutshell, setup two repositories for APT to access;
'xlibre-devuan' and 'excalibur-backports'
On reflection, decided on a much simpler method; do away with all of that previous effort. Instead, just build Easy from Devuan packages as normal, then as a final step, install a single xlibre package that will overwrite all the Devuan X11 packages. And, those Devuan packages will be put on "hold" so won't get updated.
Simple, and the single big xlibre package could be a .deb package, but instead I chose the build a .pet package. PET packages are the original native package format in Puppy Linux, still supported in the EasyOS PKGget package manager. Note, it was forum member lobster who, a long time ago, stated that PET is an acronym for "Puppy Extra Treats".
A good thing about PET packages is that APT knows nothing about them. This is something that we can take advantage of; the script '4create-pet' will create a package, named, for example 'xlibre-25.1.0-260605-amd64.pet' that, when installed, will overwrite all of the X11 files. Here is the script:
#!/bin/sh
V="$(grep -o "version: '.*" xserver/meson.build | head -n 1 | cut -f 2 -d "'")"
D0="$(date +%y%m%d)"
D="${V}-${D0}" #ex: 25.1.0-260607
[ -d xlibre-${D}-amd64 ] && rm -rf xlibre-${D}-amd64
[ -d xlibre_DEV-${D}-amd64 ] && rm -rf xlibre_DEV-${D}-amd64
[ -f xlibre-${D}-amd64.pet ] && rm -f xlibre-${D}-amd64.pet
[ -f xlibre_DEV-${D}-amd64.pet ] && rm -f xlibre_DEV-${D}-amd64.pet
cp -a image xlibre-${D}-amd64
sync
#for debian compatibility...
mv -f xlibre-${D}-amd64/usr/bin/Xorg xlibre-${D}-amd64/usr/lib/xorg/
echo '#!/bin/sh
#
# Execute Xorg.wrap if it exists otherwise execute Xorg directly.
# This allows distros to put the suid wrapper in a separate package.
basedir=/usr/lib/xorg
if [ -x "$basedir"/Xorg.wrap ]; then
exec "$basedir"/Xorg.wrap "$@"
else
exec "$basedir"/Xorg "$@"
fi' > xlibre-${D}-amd64/usr/bin/Xorg
chmod 755 xlibre-${D}-amd64/usr/bin/Xorg
find xlibre-${D}-amd64 -type f -exec sh -c 'file "$1" | grep -qE "ELF.*(executable|shared object)"' _ {} \; -exec strip --strip-unneeded {} +
sync
mkdir -p xlibre_DEV-${D}-amd64/usr/lib/xorg/modules/drivers
mkdir -p xlibre_DEV-${D}-amd64/usr/lib/xorg/modules/input
mv -f xlibre-${D}-amd64/usr/include xlibre_DEV-${D}-amd64/usr/
mv -f xlibre-${D}-amd64/usr/lib/pkgconfig xlibre_DEV-${D}-amd64/usr/lib/
mv -f xlibre-${D}-amd64/usr/lib/xorg/modules/drivers/*.la xlibre_DEV-${D}-amd64/usr/lib/xorg/modules/drivers/
mv -f xlibre-${D}-amd64/usr/lib/xorg/modules/input/*.la xlibre_DEV-${D}-amd64/usr/lib/xorg/modules/input/
sync
S="$(du -sk xlibre-${D}-amd64 | cut -f 1)"
echo "xlibre-${D}-amd64|xlibre|${D}-amd64||BuildingBlock|${S}K||xlibre-${D}-amd64.pet||Xlibre X11 server and drivers|devuan|excalibur||" > xlibre-${D}-amd64/pet.specs
S="$(du -sk xlibre_DEV-${D}-amd64 | cut -f 1)"
echo "xlibre_DEV-${D}-amd64|xlibre_DEV|${D}-amd64||BuildingBlock|${S}K||xlibre_DEV-${D}-amd64.pet||Xlibre X11 server and drivers|devuan|excalibur||" > xlibre_DEV-${D}-amd64/pet.specs
dir2tgz xlibre-${D}-amd64
tgz2pet xlibre-${D}-amd64.tar.gz
dir2tgz xlibre_DEV-${D}-amd64
tgz2pet xlibre_DEV-${D}-amd64.tar.gz
sync
echo "Created: xlibre-${D}-amd64.pet, xlibre_DEV-${D}-amd64.pet"
###end###
...the script also creates a separate 'xlibre_DEV-25.1.0-260605-amd64.pet' package.
The '4create-pet' script uploaded, with false '.gz' appended, here.
I could have created a 'pinstall.sh' post-install script inside the .pet, to put all the Devuan packages on "hold", for example:
# apt-mark hold xserver-xorg-video-vmware
However, I intend to do that in woofQ2. The xlibre PET is going to be installed into 'easy.sfs' in woofQ2, and one of the build scripts will do those "hold" operations.
Installing files without APT knowing, or removing, is done all
over the place in woofQ2, mostly as exercises to reduce the bloat
of 'easy.sfs'. So not doing anything new here.
Tags: easy